
Is your current cybersecurity strategy truly protecting your business from modern threats? In today’s complex digital landscape, traditional perimeter-based security is no longer sufficient. Enter Zero Trust, a security framework built on the principle of “never trust, always verify.” But what does that actually mean in practice?
This guide breaks down the core concepts of Zero Trust and offers actionable steps to implement it effectively, enhancing your organization’s cybersecurity posture.
What is Zero Trust Security?
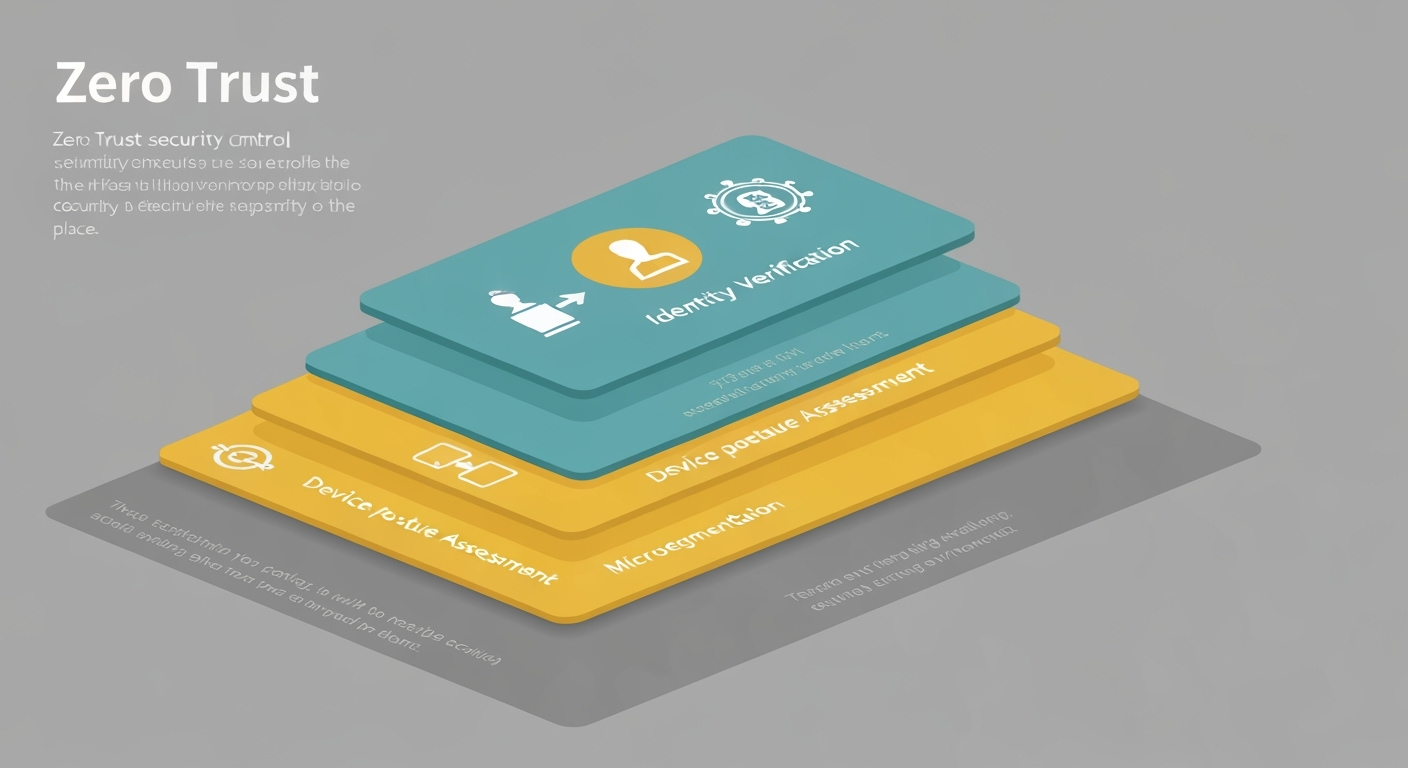
Zero Trust is a security model that assumes no user or device, whether inside or outside the network perimeter, should be automatically trusted. Instead, every access request is verified before granting access to resources.
Think of it like airport security: everyone, regardless of their role or origin, goes through screening before being allowed access to secure areas. Zero Trust applies this principle to your entire network.
Key Principles of Zero Trust
- Assume Breach: The foundation of Zero Trust is the understanding that attackers are already present (or will be) within your environment. This necessitates constant monitoring and verification.
- Explicit Verification: Every user, device, and application attempting to access resources must be authenticated and authorized. This includes verifying identity, device security posture, and user behavior.
- Least Privilege Access: Grant users only the minimum level of access required to perform their job functions. This limits the potential damage from compromised accounts.
- Microsegmentation: Divide your network into smaller, isolated segments. This restricts lateral movement for attackers, preventing them from accessing sensitive data even if they breach one segment.
- Continuous Monitoring: Continuously monitor all network traffic and user activity for suspicious behavior. Employ security information and event management (SIEM) systems and threat intelligence feeds for proactive threat detection.
Implementing Zero Trust: A Step-by-Step Approach
Implementing Zero Trust doesn’t happen overnight. It’s a journey that requires careful planning and execution. Here’s a phased approach:
- Identify Protect Surfaces: Begin by identifying your most critical data assets and the systems that protect them. These are your “protect surfaces” – focus your initial efforts here.
- Map Transaction Flows: Understand how data flows within your organization and who or what has access to it. Identify potential vulnerabilities and areas where controls are lacking.
- Architect a Zero Trust Environment: Design a security architecture that incorporates the principles of Zero Trust. This may involve implementing multi-factor authentication (MFA), network segmentation, and advanced threat detection tools.
- Implement Security Controls: Deploy the necessary security controls to enforce your Zero Trust policies. This includes identity and access management (IAM) solutions, endpoint detection and response (EDR) tools, and network firewalls.
- Monitor and Optimize: Continuously monitor the effectiveness of your Zero Trust implementation and make adjustments as needed. Regularly review your policies and procedures to ensure they remain aligned with your business needs and the evolving threat landscape.
Benefits of Zero Trust
- Reduced Attack Surface: By segmenting your network and limiting access, you reduce the potential impact of a successful attack.
- Improved Threat Detection: Continuous monitoring and analysis help you identify and respond to threats more quickly and effectively.
- Enhanced Compliance: Zero Trust aligns with many regulatory requirements, such as GDPR and HIPAA.
- Increased Agility: A Zero Trust architecture can enable greater flexibility and agility, allowing you to adapt more easily to changing business needs.
Common Challenges and How to Overcome Them
- Complexity: Implementing Zero Trust can be complex and require significant technical expertise. Solution: Partner with a qualified cybersecurity provider to guide you through the process.
- Cost: Implementing the necessary security controls can be expensive. Solution: Prioritize your efforts based on risk and start with your most critical assets.
- User Experience: Zero Trust can sometimes impact user experience. Solution: Implement user-friendly security controls and provide adequate training and support.
Conclusion
Zero Trust is not just a buzzword; it’s a fundamental shift in how we approach cybersecurity. By adopting a “never trust, always verify” mindset, you can significantly strengthen your organization’s defenses against modern threats. While the journey to Zero Trust may seem daunting, the benefits of increased security, improved compliance, and greater agility make it a worthwhile investment.